From Barista to ISO27001
 Life’s journey often takes unexpected turns, and sometimes, those twists can lead to remarkable transformations in your career. Over the past year and a bit, I have gone on a career journey that started from behind a coffee counter and ended with the privilege of leading a team of ISO 27001 internal auditors.
Not so long ago, my days were filled with the rich aroma of coffee beans and the friendly hum of customers. I was a barista, crafting cappuccinos and lattes, creating moments of warmth and connec...
Life’s journey often takes unexpected turns, and sometimes, those twists can lead to remarkable transformations in your career. Over the past year and a bit, I have gone on a career journey that started from behind a coffee counter and ended with the privilege of leading a team of ISO 27001 internal auditors.
Not so long ago, my days were filled with the rich aroma of coffee beans and the friendly hum of customers. I was a barista, crafting cappuccinos and lattes, creating moments of warmth and connec...

 0xcon is aimed at bringing together the local cyber security community to share knowledge and to network with like minded individuals. This event is very much by the community for the community, so whether you’re a seasoned expert or just starting out, we would love to welcome you to our conference as we enhance our understanding of the cyber security landscape. The conference covers a wide array of topics including cyber security best practices, threat intelligence, IOT security, ransomware, incident re...
0xcon is aimed at bringing together the local cyber security community to share knowledge and to network with like minded individuals. This event is very much by the community for the community, so whether you’re a seasoned expert or just starting out, we would love to welcome you to our conference as we enhance our understanding of the cyber security landscape. The conference covers a wide array of topics including cyber security best practices, threat intelligence, IOT security, ransomware, incident re... Bsides Cape Town 2022 is a month away. We are excited to finally have Cape Town’s hacker summer camp and year end in person again. We have some really exciting speakers and a workshop.
How to participate
Get your tickets: https://qkt.io/M9YKVw
Keep an eye on our youtube channel:
Buy a hoodie: https://qkt.io/M9YKVw (Merchandise to be fetched on the day)
Location
Map: Google Maps
Venue: https://tobmce.co.za/
More about venue: https://bsidescapetown.co.za/bsides-conf/2022-location
Event Program
...
Bsides Cape Town 2022 is a month away. We are excited to finally have Cape Town’s hacker summer camp and year end in person again. We have some really exciting speakers and a workshop.
How to participate
Get your tickets: https://qkt.io/M9YKVw
Keep an eye on our youtube channel:
Buy a hoodie: https://qkt.io/M9YKVw (Merchandise to be fetched on the day)
Location
Map: Google Maps
Venue: https://tobmce.co.za/
More about venue: https://bsidescapetown.co.za/bsides-conf/2022-location
Event Program
... As many people in the InfoSec community are aware - getting your OSCP is something life-changing. Worldwide, there are a vast number of individuals who understand what a golden opportunity it is to complete the PWK course, even more so when it’s free.
Yes, FREE! No strings attached. We just want our community to succeed.
HOW IT STARTED:
Following the death of George Floyd, Offensive Security created their Social Responsibility Program. One of the goals of this program was to provide sets of PEN...
As many people in the InfoSec community are aware - getting your OSCP is something life-changing. Worldwide, there are a vast number of individuals who understand what a golden opportunity it is to complete the PWK course, even more so when it’s free.
Yes, FREE! No strings attached. We just want our community to succeed.
HOW IT STARTED:
Following the death of George Floyd, Offensive Security created their Social Responsibility Program. One of the goals of this program was to provide sets of PEN... Red Teaming - My first physical assessment
By chrismeistre
I’ve recently been given the opportunity to perform my first physical assessment during a black box engagement for a client.
In short, the black box permitted us to try anything to gain access to their infrastructure, and assess their IT security awareness and defenses.
I was excited about this, and when the time finally came, I wasn’t left wanting.
If you’re reading this as an aspiring hacker, or just someone interested in cyber security o...
Red Teaming - My first physical assessment
By chrismeistre
I’ve recently been given the opportunity to perform my first physical assessment during a black box engagement for a client.
In short, the black box permitted us to try anything to gain access to their infrastructure, and assess their IT security awareness and defenses.
I was excited about this, and when the time finally came, I wasn’t left wanting.
If you’re reading this as an aspiring hacker, or just someone interested in cyber security o... My journey into cyber security/infosec.
By Sp3ctrlM0nki3
So, I’ll start at the beginning. My passion for cyber sec started in a computer lab in high school where I created my first ‘virus’. It was a little .bat virus which would remove the System 32 Folder from your windows system.
del c:WINDOWSsystem32*.*/q [1]
My journey into cyber security/infosec.
By Sp3ctrlM0nki3
So, I’ll start at the beginning. My passion for cyber sec started in a computer lab in high school where I created my first ‘virus’. It was a little .bat virus which would remove the System 32 Folder from your windows system.
del c:WINDOWSsystem32*.*/q [1]
 Vortimo is the brain child of Roelof Temmingh, the man that brought us Maltego. On Wednesday 4 August 2021 he will be giving us a demo on his new OSINT web augmentation tool, Vortimo! Vortimo has many uses and functions, some of which we will cover on Wednesday. We can break down certain functions by what we find on their site
Vortimo is the brain child of Roelof Temmingh, the man that brought us Maltego. On Wednesday 4 August 2021 he will be giving us a demo on his new OSINT web augmentation tool, Vortimo! Vortimo has many uses and functions, some of which we will cover on Wednesday. We can break down certain functions by what we find on their site
 I’ve recently swapped out playing CTFs in my free time to trying to catch bugs in my free time, usually for a bounty. Since bug bounty platforms are usually focused on web or mobile applications, I thought it might be interesting to introduce an emerging branch of bug bounty, focusing on smart contracts.
I’ve recently swapped out playing CTFs in my free time to trying to catch bugs in my free time, usually for a bounty. Since bug bounty platforms are usually focused on web or mobile applications, I thought it might be interesting to introduce an emerging branch of bug bounty, focusing on smart contracts.
 Recently I was doing a Pentest, and I realised I am such a wannabe pentester, and I say this because I had to reach out my friends at Hack South for help on basic things.
I am a jack of all trades, master of none, and so, I do not know many things by heart especially when not used on a
daily basis.
Recently I was doing a Pentest, and I realised I am such a wannabe pentester, and I say this because I had to reach out my friends at Hack South for help on basic things.
I am a jack of all trades, master of none, and so, I do not know many things by heart especially when not used on a
daily basis.
 The United Nations Cybercrime Unit in Africa, lead by Carmen Corbin_UN created a unique Digital Forensics CTF competition for the month of May. This was only open for the African continent for people who are keen to see how their skills are in the digital forensics cybersecurity field. I for one do not work in the digital forensics field so I wanted to see how I would do in this but having worked as a systems administrator for most of my career, and now trying to make a move into offensive / forensics se...
The United Nations Cybercrime Unit in Africa, lead by Carmen Corbin_UN created a unique Digital Forensics CTF competition for the month of May. This was only open for the African continent for people who are keen to see how their skills are in the digital forensics cybersecurity field. I for one do not work in the digital forensics field so I wanted to see how I would do in this but having worked as a systems administrator for most of my career, and now trying to make a move into offensive / forensics se... Table of Contents
Introduction
Experience
Pre-OSCP
PWK Labs
Post-Labs
Exam
Conclusion
Pay It Forward – PWK Vouchers
Resources
Pre-OSCP Resources
PWK Labs Resources
Post-Labs Resources
Exam Resources
Introduction
So you are planning to pursue the Offensive Security Certified Professional (OSCP) certification and are thinking about starting the Penetration Testing with Kali Linux (PWK) labs. This post covers some additional OSCP preparation that y...
Table of Contents
Introduction
Experience
Pre-OSCP
PWK Labs
Post-Labs
Exam
Conclusion
Pay It Forward – PWK Vouchers
Resources
Pre-OSCP Resources
PWK Labs Resources
Post-Labs Resources
Exam Resources
Introduction
So you are planning to pursue the Offensive Security Certified Professional (OSCP) certification and are thinking about starting the Penetration Testing with Kali Linux (PWK) labs. This post covers some additional OSCP preparation that y... Intro
Just over a year ago, having participated in a few Digital Forensics and Incident Response (DFIR) Capture The Flag (CTF) challenges, I started an internal one at work.
This was aimed at Security Operation Center (SOC) and DFIR analysts, while using actual alert data from our environment. The great thing about this was the ability to present analysts with the same data they work on during normal operations. This meant we could test their understanding of what they were seeing, all while having the ...
Intro
Just over a year ago, having participated in a few Digital Forensics and Incident Response (DFIR) Capture The Flag (CTF) challenges, I started an internal one at work.
This was aimed at Security Operation Center (SOC) and DFIR analysts, while using actual alert data from our environment. The great thing about this was the ability to present analysts with the same data they work on during normal operations. This meant we could test their understanding of what they were seeing, all while having the ... I competed in DawgCTF with the Hack South CTF team on 8 May 2021. This is an 24-hour, entry-level CTF hosted by University of Maryland, Baltimore County’s CyberDawgs. We ended up placing 28th overall.
Here are the write-ups for the four challenges I solved.
I competed in DawgCTF with the Hack South CTF team on 8 May 2021. This is an 24-hour, entry-level CTF hosted by University of Maryland, Baltimore County’s CyberDawgs. We ended up placing 28th overall.
Here are the write-ups for the four challenges I solved.
 A journey through my first rookie talk, how I prepped for it and the details behind the amazing con, which happened on the weekend of the 17th and the 18th of April 2021.
I spoke about a topic close to me, namely the usage of technology in business, or as I put it: “Bizops in Motion”.
2021 is a year of opportunity. Let’s make the most of this year.
More posts to come!
A journey through my first rookie talk, how I prepped for it and the details behind the amazing con, which happened on the weekend of the 17th and the 18th of April 2021.
I spoke about a topic close to me, namely the usage of technology in business, or as I put it: “Bizops in Motion”.
2021 is a year of opportunity. Let’s make the most of this year.
More posts to come!
 Hack South is first and foremost a community of people based in South Africa but open to the world. Our growing community has a great variety of members, some of which are passionate information security practitioners, open-source investigators, developers, digital rights advocates and some are from a variety of other fields (even some totally unrelated to computers).
Hack South is first and foremost a community of people based in South Africa but open to the world. Our growing community has a great variety of members, some of which are passionate information security practitioners, open-source investigators, developers, digital rights advocates and some are from a variety of other fields (even some totally unrelated to computers).
 On the weekend of the 22nd, I participated once more in the TraceLabs OSINT CTF. For context, this CTF is a bit different from other CTF's. It's not something where you compromise machines or map some networks. It's something where you actually try to dig up as much information as possible on missing people, as per the cases provided to TraceLabs by various law enforcement departments.
On the weekend of the 22nd, I participated once more in the TraceLabs OSINT CTF. For context, this CTF is a bit different from other CTF's. It's not something where you compromise machines or map some networks. It's something where you actually try to dig up as much information as possible on missing people, as per the cases provided to TraceLabs by various law enforcement departments.
.jpg) “Don’t watch the video I inboxed you, my FB has been Hacked by Hackers!”
Seen this before? Seen this more than once? You probably have. Accounts on Facebook have been hacked and taken over by hackers and they are working hard to hack your friends and families accounts… Or have they? Are they really? Who are these Hackers? And whilst we are on this subject, what are Hackers?
Read further to understand what is usually actually going on, who is doing all these account takeovers and what the differen...
“Don’t watch the video I inboxed you, my FB has been Hacked by Hackers!”
Seen this before? Seen this more than once? You probably have. Accounts on Facebook have been hacked and taken over by hackers and they are working hard to hack your friends and families accounts… Or have they? Are they really? Who are these Hackers? And whilst we are on this subject, what are Hackers?
Read further to understand what is usually actually going on, who is doing all these account takeovers and what the differen... After many years of faithful service, Adobe announced in 2017 it would discontinue support for Adobe Flash from 31 December 2020 and blocked Flash content from running in Flash Player.Many have been caught unprepared.
The South African Revenue Service (SARS) recently announced it would start using its own browser. We aim to tackle the challenge this presents and what to think about and also why with a 2+ year warning things are not in place.
After many years of faithful service, Adobe announced in 2017 it would discontinue support for Adobe Flash from 31 December 2020 and blocked Flash content from running in Flash Player.Many have been caught unprepared.
The South African Revenue Service (SARS) recently announced it would start using its own browser. We aim to tackle the challenge this presents and what to think about and also why with a 2+ year warning things are not in place.
 I had the distinct privilege of being interviewed on eNCA yesterday !
eNCA -- a.k.a. e-News Channel Africa -- is the first and most watched news service in South Africa. You can imagine that it came as a bit of a shocker to me to receive a message request in my Twitter DM's from one of their guest bookers, asking me if I'd like to come on and discuss these policy changes. So I decided to do it:
I had the distinct privilege of being interviewed on eNCA yesterday !
eNCA -- a.k.a. e-News Channel Africa -- is the first and most watched news service in South Africa. You can imagine that it came as a bit of a shocker to me to receive a message request in my Twitter DM's from one of their guest bookers, asking me if I'd like to come on and discuss these policy changes. So I decided to do it:
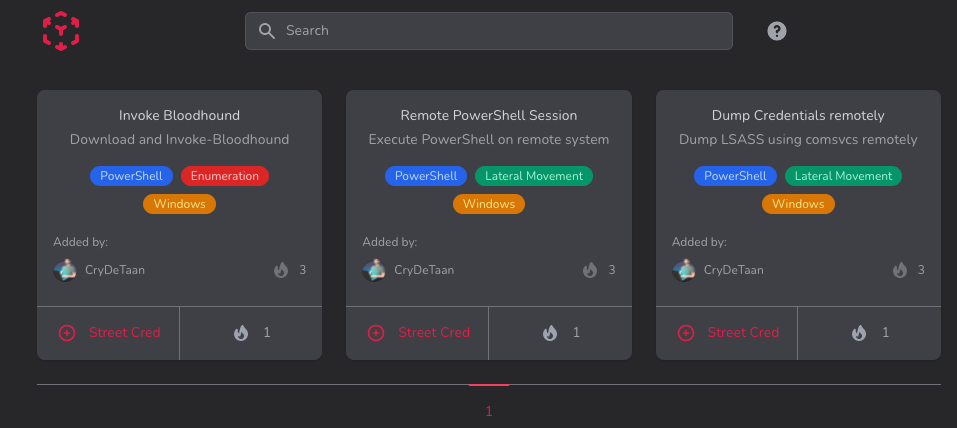
 The Hack The Box Meetup is a monthly online event hosted on the first Tuesday of every month by Hack South. The meetup is an opportunity to connect with other InfoSec enthusiasts, learn new tools and tricks, exchange knowledge and of course Hack The Box.
The Hack The Box Meetup is a monthly online event hosted on the first Tuesday of every month by Hack South. The meetup is an opportunity to connect with other InfoSec enthusiasts, learn new tools and tricks, exchange knowledge and of course Hack The Box.
 What is Hack South? Many have asked, what is Hack South, why Hack South and where is this all going? This blog will try to lay out the foundation, the activity and the vision for Hack South, Home of the ubiquitous South.
We will also highlight some things we are working on, highlight some roles, channels and activities.
What is Hack South? Many have asked, what is Hack South, why Hack South and where is this all going? This blog will try to lay out the foundation, the activity and the vision for Hack South, Home of the ubiquitous South.
We will also highlight some things we are working on, highlight some roles, channels and activities.
 A few weeks ago, a rag tag motley crew from Hack South took part in the TraceLabs missing persons CTF as part of conINT 2020. It was our 4th shot as team Hack South, but this time we scored a podium finish and just missed out on 2nd place. This is the story of how we did it, with no case specifics.
A few weeks ago, a rag tag motley crew from Hack South took part in the TraceLabs missing persons CTF as part of conINT 2020. It was our 4th shot as team Hack South, but this time we scored a podium finish and just missed out on 2nd place. This is the story of how we did it, with no case specifics.
 This post summarises the Meetup held on 1 December 2020.
Agenda
An introductory presentation on Software Reverse Engineering. A theory presentation will cover the types of outputs reverse engineers may investigate for CTFs and in practice. De-obfuscation, disassembly and decomplication will be discussed. We will look at the difference between static and dynamic analysis and how to use some of the common tools. The second half of the Meetup will feature two practical challenges: One guided, for attendees...
This post summarises the Meetup held on 1 December 2020.
Agenda
An introductory presentation on Software Reverse Engineering. A theory presentation will cover the types of outputs reverse engineers may investigate for CTFs and in practice. De-obfuscation, disassembly and decomplication will be discussed. We will look at the difference between static and dynamic analysis and how to use some of the common tools. The second half of the Meetup will feature two practical challenges: One guided, for attendees...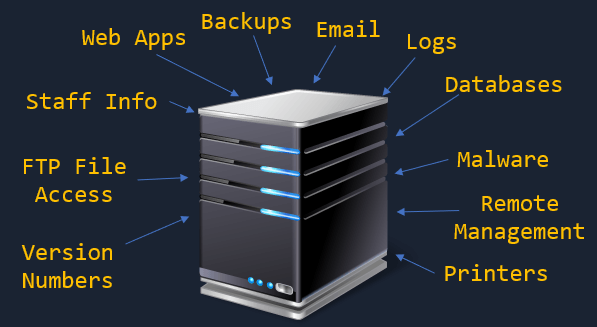 This post summarises the Meetup held on 6 October 2020.
Agenda
An introductory session focussed on the first step when beginning on a new box: enumeration. A short presentation and a live demo will introduce on the theory and practice of initial enumeration and commonly used tools. Two Hack The Box 1-month VIP vouchers will be awarded to the top two contestants in a multiple-choice quiz! The second half of the Meetup will be dedicated to hacking together on the lab while sharing tips, tricks and advice.
This post summarises the Meetup held on 6 October 2020.
Agenda
An introductory session focussed on the first step when beginning on a new box: enumeration. A short presentation and a live demo will introduce on the theory and practice of initial enumeration and commonly used tools. Two Hack The Box 1-month VIP vouchers will be awarded to the top two contestants in a multiple-choice quiz! The second half of the Meetup will be dedicated to hacking together on the lab while sharing tips, tricks and advice.
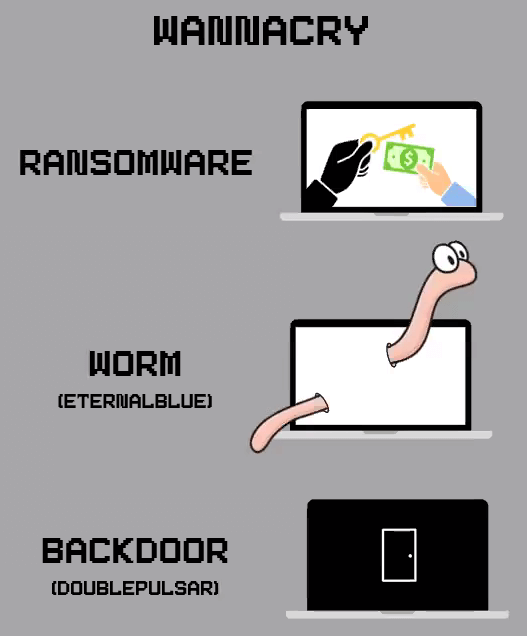 This post summarises the Meetup held on Tuesday 1 Sept 2020.
Agenda
An introductory session with the goal of getting everyone to pop a shell with EternalBlue. The backstory of WannaCry will be presented after a quick introduction. Then we will walk through the EternalBlue exploit and help everyone practice it in the HTB lab. Advanced attendees can skip forward to do other boxes on the private lab provided by HTB. The hosts will focus on walking new people through getting registered, set up, connected, a...
This post summarises the Meetup held on Tuesday 1 Sept 2020.
Agenda
An introductory session with the goal of getting everyone to pop a shell with EternalBlue. The backstory of WannaCry will be presented after a quick introduction. Then we will walk through the EternalBlue exploit and help everyone practice it in the HTB lab. Advanced attendees can skip forward to do other boxes on the private lab provided by HTB. The hosts will focus on walking new people through getting registered, set up, connected, a...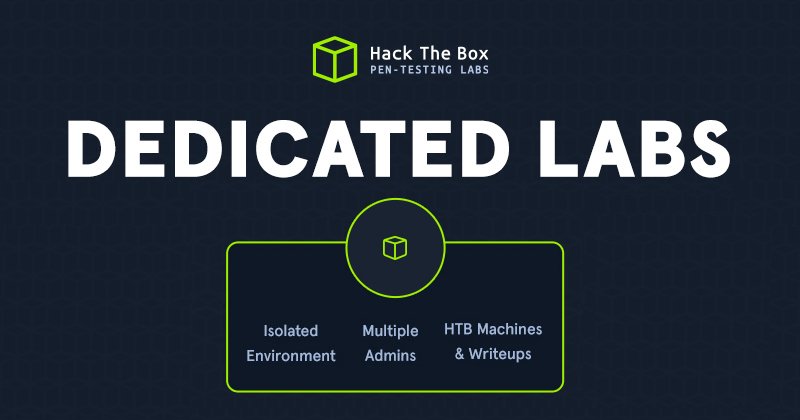 This post shows how to access our dedicated lab during Hack The Box Meetups. Instead of playing on public instances, Hack The Box provides us a private lab environment for our Meetups. A mix of active and retired machines will be available without noise or interruption from other HTB players beyond our group.
This post shows how to access our dedicated lab during Hack The Box Meetups. Instead of playing on public instances, Hack The Box provides us a private lab environment for our Meetups. A mix of active and retired machines will be available without noise or interruption from other HTB players beyond our group.
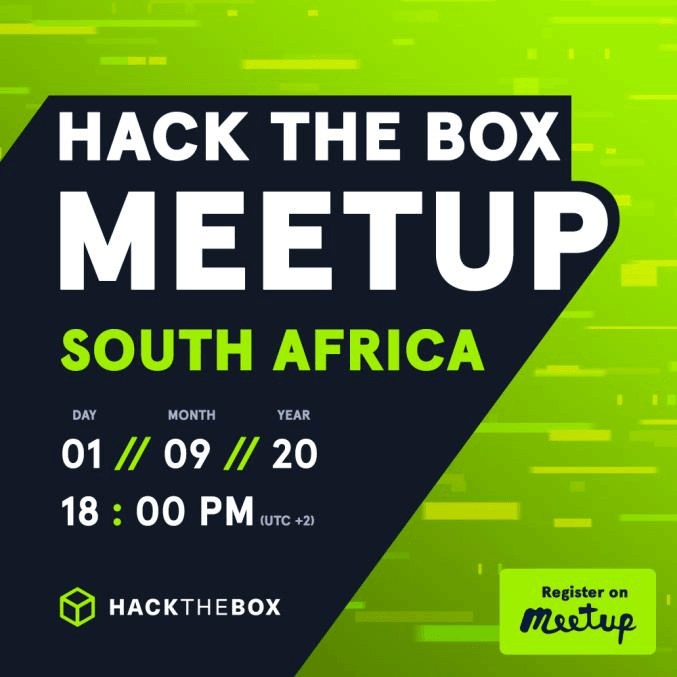 We are excited to announce the first official Hack The Box Meetup in South Africa. All meetings will be online due to Covid-19. Our first meeting will be on Tuesday 1 September, followed by monthly meetings on the first Tuesday of every month. Hack The Box is an online platform to test and advance your skills in penetration testing and cyber security. Join and RSVP for the meeting now!
We are excited to announce the first official Hack The Box Meetup in South Africa. All meetings will be online due to Covid-19. Our first meeting will be on Tuesday 1 September, followed by monthly meetings on the first Tuesday of every month. Hack The Box is an online platform to test and advance your skills in penetration testing and cyber security. Join and RSVP for the meeting now!